1、检查系统内核是否支持MPPE
modprobe ppp-compress-18 && echo OK
显示OK说明系统支持MPPE
2、检查系统是否开启TUN/TAP支持
cat /dev/net/tun
cat: /dev/net/tun: 文件描述符处于错误状态
如果这条指令显示结果为下面的文本,则表明通过
3、 检查PPP是否支持MPPE
strings ‘/usr/sbin/pppd’|grep -i mppe|wc -l
43如果以上命令输出为“0”则表示不支持;输出为“30”或更大的数字就表示支持.
4、安装ppp和iptables #PPTP需要这两个软件包,一般centOS自带
yum install -y ppp iptables
5、安装PPTP
yum install epel-release
yum install pptpd
6、配置PPTP
(1)vi /etc/ppp/options.pptpd #编辑,保存
name pptpd #自行设定的VPN服务器的名字,可以任意
#refuse-pap #拒绝pap身份验证
#refuse-chap #拒绝chap身份验证
#refuse-mschap #拒绝mschap身份验证
require-mschap-v2 #为了最高的安全性,我们使用mschap-v2身份验证方法
require-mppe-128 #使用128位MPPE加密
ms-dns 8.8.8.8 #设置DNS
ms-dns 8.8.4.4
proxyarp #启用ARP代理,如果分配给客户端的IP与内网卡同一个子网
#debug #关闭debug
lock
nobsdcomp
novj
novjccomp
#nologfd #不输入运行信息到stderr
logfile /var/log/pptpd.log #存放pptpd服务运行的的日志
(2)vi /etc/ppp/chap-secrets #编辑,保存
kuaile pptpd 666666 * #设置用户名:test 密码:123456
或者
vpnuser add kuaile 666666
(3)vi /etc/pptpd.conf #编辑,保存
option /etc/ppp/options.pptpd
logwtmp
localip 10.0.6.1 #设置VPN服务器虚拟IP地址
remoteip 10.0.6.101-200 #为拨入VPN的用户动态分配10.0.6.101~10.0.0.200之间的IP
7. 开启系统路由模式
sysctl net.ipv4.ip_forward
net.ipv4.ip_forward = 0
vi /etc/sysctl.conf #编辑
net.ipv4.ip_forward = 1 #找到此行 去点前面#,把0改成1 开启路由模式,如果没有就自行添加
/sbin/sysctl -p #使设置立刻生效
sysctl net.ipv4.ip_forward
net.ipv4.ip_forward = 1
7、配置防火墙NAT转发
centos 7 默认采用firewalld动态防火墙,我还是更习惯使用iptables
yum install iptables-services
systemctl stop firewalld.service
systemctl disable firewalld.service
yum erase firewalld
systemctl enable iptables.service
systemctl start iptables.servic
开启包转发
iptables -t nat -A POSTROUTING -s 10.0.6.0/24 -o eth0 -j MASQUERADE
意思是对即将发送出去的数据包进行修改,对来自设备eth0且源地址是10.0.6.0/24的数据包,把源地址修改为主机地址及vPN地址
iptables -t nat -L #完成后可以查看NAT表是否已经生效
这里要注意服务器的网口不一定是eth0,用netstat -i 查看
service iptables save #保存防火墙设置
service restart #重启防火墙
对于开启了iptables过滤的主机,需要开放VPN服务的端口:1723 和gre协议
使用一下命令添加
开放pptp使用的1723端口和gre协议
iptables -A INPUT -p tcp -m state --state NEW,RELATED,ESTABLISHED -m tcp --dport 1723 -j ACCEPT iptables -A INPUT -p gre -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT
iptables -t nat -A POSTROUTING -s 10.0.6.0/24 -o eth0 -j MASQUERADE
或者(这俩条应该是等效的,一种不行的话, 用另一种试试)
iptables -t nat -A POSTROUTING -s 10.0.6.0/24 -o eth0 -j SNAT –to 你的主机IP
iptables -A FORWARD -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
##############################################################################################################################
如果iptables规则中有拒绝的选项,需要注意接受的要在拒绝的前面。
Centos 7 的iptables默认规则中就有
-A INPUT -j REJECT --reject-with icmp-host-prohibited-A FORWARD -j REJECT --reject-with icmp-host-prohibited添加的规则一定要在这条规则的前面,所以用插入的方法添加规则
iptables -I INPUT 5 -p tcp -m state --state NEW -m tcp --dport 1723 -j ACCEPTiptables -I INPUT 6 -p tcp -m state --state NEW -m tcp --dport 47 -j ACCEPTiptables -I INPUT 7 -p gre -m state --state NEW -j ACCEPTiptables -I FORWARD 2 -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT iptables -I FORWARD 3 -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -t nat -A POSTROUTING -s 10.0.6.0/24 -o eth0 -j MASQUERADE
添加完成后试用iptalbes命令检查一下
[root@Centos7 ~]# iptables -LChain INPUT (policy ACCEPT)target prot opt source destinationDROP all -- anywhere anywhere state INVALIDACCEPT icmp -- anywhere anywhereACCEPT all -- anywhere anywhereACCEPT tcp -- anywhere anywhere state NEW,RELATED,ESTABLISHED tcp dpt:sshACCEPT tcp -- anywhere anywhere state NEW,RELATED,ESTABLISHED tcp dpt:pptpACCEPT gre -- anywhere anywhere state NEW,RELATED,ESTABLISHEDACCEPT all -- anywhere anywhere state RELATED,ESTABLISHEDREJECT all -- anywhere anywhere reject-with icmp-host-prohibitedChain FORWARD (policy ACCEPT)target prot opt source destinationDROP all -- anywhere anywhere state INVALIDACCEPT all -- anywhere anywhere state NEW,RELATED,ESTABLISHEDACCEPT all -- anywhere anywhere state RELATED,ESTABLISHEDREJECT all -- anywhere anywhere reject-with icmp-host-prohibitedChain OUTPUT (policy ACCEPT)target prot opt source destinationDROP all -- anywhere anywhere state INVALID
[root@Centos7 ~]# iptables -t nat -LChain PREROUTING (policy ACCEPT)target prot opt source destinationChain POSTROUTING (policy ACCEPT)target prot opt source destinationMASQUERADE all -- 10.0.6.0/24 anywhereChain OUTPUT (policy ACCEPT)target prot opt source destination
没问题后可以保存一下
service iptables save
这是我设置iptables的全部命令,供参考
888是我修改的ssh端口号
/sbin/iptables -F /sbin/iptables -Z /sbin/iptables -P INPUT ACCEPT /sbin/iptables -A INPUT -m state --state INVALID -j DROP /sbin/iptables -A INPUT -p icmp -j ACCEPT /sbin/iptables -A INPUT -i lo -j ACCEPT /sbin/iptables -A INPUT -p tcp -m state --state NEW,RELATED,ESTABLISHED -m tcp --dport 888 -j ACCEPT /sbin/iptables -A INPUT -p tcp -m state --state NEW,RELATED,ESTABLISHED -m tcp --dport 1723 -j ACCEPT /sbin/iptables -A INPUT -p gre -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT /sbin/iptables -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT /sbin/iptables -A INPUT -j REJECT --reject-with icmp-host-prohibited /sbin/iptables -P FORWARD ACCEPT /sbin/iptables -A FORWARD -m state --state INVALID -j DROP /sbin/iptables -A FORWARD -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT /sbin/iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT /sbin/iptables -A FORWARD -j REJECT --reject-with icmp-host-prohibited /sbin/iptables -P OUTPUT ACCEPT /sbin/iptables -A OUTPUT -m state --state INVALID -j DROP /sbin/iptables -F -t nat /sbin/iptables -Z -t nat /sbin/iptables -t nat -A POSTROUTING -s 10.0.6.0/24 -o seth0 -j MASQUERADE
这是我的iptabls规则文件
[root@Centos7 ~]# cat /etc/sysconfig/iptables# Generated by iptables-save v1.4.7 on Fri Nov 28 15:27:36 2014*filter:INPUT ACCEPT [0:0]:FORWARD ACCEPT [0:0]:OUTPUT ACCEPT [67:9660]-A INPUT -m state --state INVALID -j DROP-A INPUT -p icmp -j ACCEPT-A INPUT -i lo -j ACCEPT-A INPUT -p tcp -m state --state NEW,RELATED,ESTABLISHED -m tcp --dport 888 -j ACCEPT-A INPUT -p tcp -m state --state NEW,RELATED,ESTABLISHED -m tcp --dport 1723 -j ACCEPT-A INPUT -p gre -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT-A INPUT -j REJECT --reject-with icmp-host-prohibited-A FORWARD -m state --state INVALID -j DROP-A FORWARD -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT-A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT-A FORWARD -j REJECT --reject-with icmp-host-prohibited-A OUTPUT -m state --state INVALID -j DROPCOMMIT# Completed on Fri Nov 28 15:27:36 2014# Generated by iptables-save v1.4.7 on Fri Nov 28 15:27:36 2014*nat:PREROUTING ACCEPT [7:1301]:POSTROUTING ACCEPT [0:0]:OUTPUT ACCEPT [0:0]-A POSTROUTING -s 10.0.6.0/24 -o seth0 -j MASQUERADECOMMIT# Completed on Fri Nov 28 15:27:36 2014
8、设置PPTP开机启动
service pptpd start #启动pptpd
systemctl enabled pptpd #设置开机启动
pptpd服务使用的端口是1723,这个端口是系统固定分配的,可以通过查看该端口检查pptpd服务的运行情况。
命令:netstat -ntpl
[root@Centos7 ~]# netstat -ntpl
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN 1423/cupsd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 1693/master
tcp 0 0 0.0.0.0:44666 0.0.0.0:* LISTEN 1358/rpc.statd
tcp 0 0 0.0.0.0:1723 0.0.0.0:* LISTEN 2020/pptpd
tcp 0 0 0.0.0.0:66 0.0.0.0:* LISTEN 1579/sshd
tcp 0 0 0.0.0.0:111 0.0.0.0:* LISTEN 1310/rpcbind
tcp 0 0 ::1:631 :::* LISTEN 1423/cupsd
tcp 0 0 ::1:25 :::* LISTEN 1693/master
tcp 0 0 :::66 :::* LISTEN 1579/sshd
tcp 0 0 :::33794 :::* LISTEN 1358/rpc.statd
tcp 0 0 :::111 :::* LISTEN 1310/rpcbind
至此,VPN服务器搭建完成.
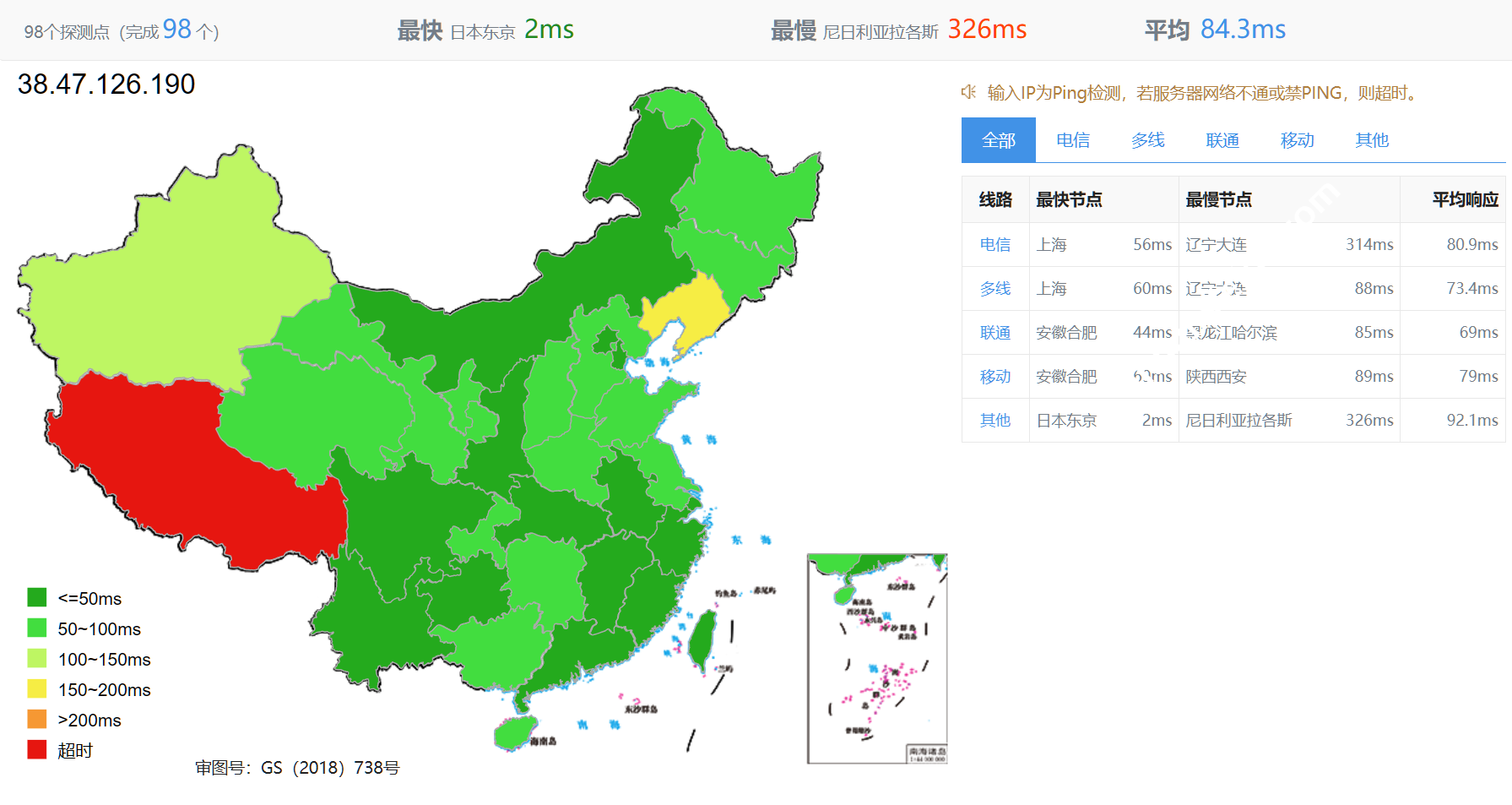
 CNIDC测评
CNIDC测评